Water utilities are prime targets for cyberattacks! Their systems are getting more complex and interconnected which can make it overwhelming for utilities. It’s easy for us to say “Oh, that will never happen to us”. Be wary of any false confidence as recent incidents found and exposed flows at utilities.
“About 70 percent of utilities inspected by federal officials over the last year violated standards meant to prevent breaches or other intrusions” - The EPA
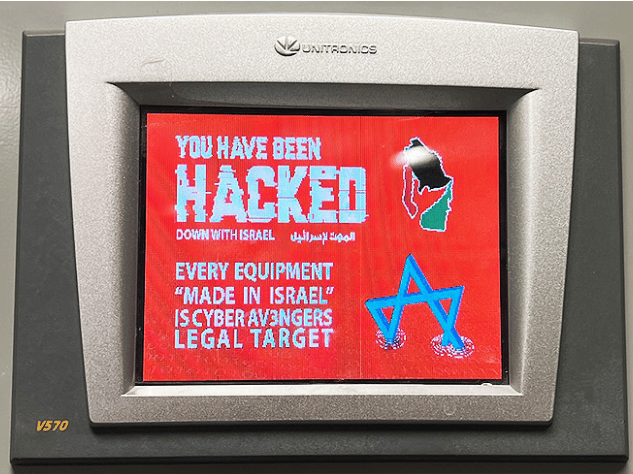
Cyber Av3ngers Hack
Oldsmar Water Treatment Plant, Florida - In February 2021, a hacker gained remote access to the plant's computer system and attempted to increase the levels of sodium hydroxide (lye) to dangerous levels. No harm was caused as an operator quickly noticed the intrusion and reversed the chemical levels. However, it highlighted the vulnerability of remote access systems. The plant used an outdated Windows operating system and allowed remote access through a shared password, making it easy for the hacker to gain entry.
Water Treatment Plant in the San Francisco Bay Area - In January 2021, a hacker breached a water treatment plant serving the Bay Area by exploiting a former employee's TeamViewer account credentials. The hacker deleted programs used for water treatment, but no failures or illnesses were reported. The security failure was unrevoked access credentials for former employees, allowing the hacker to use stolen login information.
Municipal Water Authority of Aliquippa, Pittsburgh - In 2023, the Iran-backed hacking group "Cyber Av3ngers" attacked this water utility, shutting down systems that monitor water pressure at a booster station. The attack forced the water company to switch to manual monitoring of water pressure. Vulnerable internet-connected devices manufactured in Israel were targeted, highlighting the risks of using insecure IoT devices in critical infrastructure.
Understanding the Threat Landscape
There is a range of cyber threats, including malware, ransomware, and targeted attacks aimed at disrupting operations or compromising water quality. The complexity of water systems, which often integrate operational technology (OT) with information technology (IT), presents unique risks. With a single cyber security breach all the below can be impacted:
Public Health Hazards: Manipulating chemical levels in water treatment processes can lead to severe health risks, including poisoning and long-term health effects.
Operational Disruption: Cyberattacks can disrupt the operation of water treatment and distribution systems, leading to service outages and emergency responses.
Data Breaches: Compromising customer data can result in privacy violations and financial losses.
Environmental Damage: Attacks on treatment facilities can cause significant environmental pollution and damage.
Economic Costs: Cyberattacks often result in substantial financial costs due to remediation, legal liabilities, and loss of public trust.
Implementing Cybersecurity Measures
Risk Assessment: Begin with a thorough risk assessment to identify vulnerabilities and potential threats. The AWWA provides guidelines for conducting cybersecurity assessments tailored to water utilities, helping to pinpoint critical assets and high-risk areas. Implementation: AWWA Cybersecurity Guidance
Developing a Cybersecurity Plan: Based on the assessment, develop a cybersecurity plan. This plan should include policies, procedures, and controls designed to mitigate identified risks. Implementation: Either assign someone internally to learn or get outside support to document your approach and make sure everyone knows their area of responsibility.
Network Segmentation: Segment OT and IT networks to limit the spread of cyber threats. This involves creating isolated network zones for critical systems and implementing strict access controls. Implementation: Use firewalls and virtual LANs (VLANs) to separate SCADA systems from corporate networks.
Access Controls: Implement robust access control measures to ensure that only authorized personnel can access critical systems. This includes multi-factor authentication (MFA) and role-based access control (RBAC). Implementation: Implement MFA for accessing control systems and use RBAC to restrict access based on job roles. It’s important to manage this for outside vendors and technology subscriptions.
Regular Updates and Patch Management: Keep all systems and software up to date with the latest security patches. Vulnerabilities in outdated software are a common entry point for cyberattacks. Implementation: Work across all systems for a responsibilities checklist of internal vs vendor patch management scheduling and rotating security checks.
Employee Training and Awareness: Train employees on cybersecurity best practices and the importance of vigilance. Regular training sessions can help staff recognize phishing attempts and other common attack vectors. Implementation: Conduct annual cybersecurity training and periodic phishing simulation exercises. It’s better to capture any oversights in security up front rather than have someone else discover them.
Continuous Monitoring: Implement continuous monitoring tools to detect and respond to suspicious activities in real-time. Security Information and Event Management (SIEM) systems can aggregate and analyze logs from various sources. Implementation: Deploy a SIEM solution to monitor network traffic and system logs for anomalies. Most utilities IT departments can utilize Microsoft Sentinel or another solution.
Incident Response: Develop and test incident response plans to ensure swift action in the event of a cyber incident. Regular drills and updates to the plan are essential for preparedness. Implementation: Conduct regular tabletop exercises to simulate cyber incidents and refine response strategies. It’s best to schedule these on a regular basis such as each quarter as you will need operations, IT, and OT all working together.
Backup and Recovery: Ensure that all critical data is backed up regularly and that recovery procedures are in place. Backups should be stored securely and tested periodically. Even when using large cloud providers there is a risk of loss. Implementation: Implement a 3-2-1 backup strategy (three copies of data, on two different media, with one copy off-site).

Don’t let this be your security policy
In case you missed it, AWWA and AMWA are pushing back against blanket PFAS regulations.
Know someone who could benefit from this info? Forward this newsletter to them!
Make sense to connect?
Are you working to help your utility or technology company take the next step forward? If you want to talk through a challenge or share something interesting your team did please shoot me a note at [email protected] or schedule a utility technology review here.